Deploy YubiKey hardware MFA devices faster with ID proofing workflows, single step secure encoding, an automatic reporting manager and self-service dashboards.
IdExchange provides enterprise capabilities not available in traditional YubiKey manager software
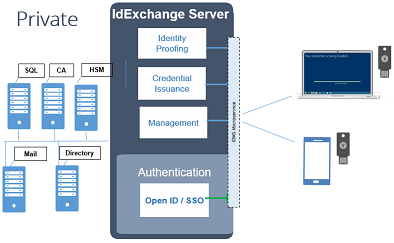
IdExchange is a private platform that is easy to install in your cloud that provides easy-to-use wizards, auditable workflows, and direct PKI integrations to drastically make it easier for organizations to issue YubiKey devices across a large enterprise.
ID Proof
Perform ID proofing prior to issuance to make sure the YubiKey is being deployed and associated with the correct person.
Encode
IdExchange uses the secure channel protocol to change card management keys and loads certificates with a single button push.
Report
A enterprise reporting dashboard helps you keep track of issued YubiKey devices for performance and compliance needs.
Maintain
Provide post management services to enable users to change their PIN, update certificates, or replace their YubiKey.
| Features at a glance | ||
|---|---|---|
| WORKFLOW | TECHNICAL | REPORTING |
| Identity proofing | Custom CSR | Chain of trust |
| Device Verification | Custom FIDO | Enterprise reporting |
| Workflow approvals | Key attestation | Device Inventory |
| Device Unlock | Management key changed | Aging |
| Remote Issuance | Single Step OTP consolidation | Officer Action |
Designed to Accelerate YubiKey Deployment
From PKI automation to remote issuance models, IdExchange enhances the YubiKey Manager with the tools and control to scale your YubiKey deployment with speed.
Single Step Certificate Loading
Tap in to the YubiKey Manager APIs to streamline certificate issuance. Provide custom data for subject alternative names, email addresses and certificate expiration dates to generate the perfect certificate for your MFA use case.
Automated Device Security
Ensure your YubiKey devices are locked down by automatically switching their default management keys with secure keys from your HSM.
Self-service tools
The IdExchange self service portal makes it easy for your workforce to encode their YubiKey from anywhere they are located…even directly from a mobile phone.
ID System Synching
Eliminate manual retrieval of identity data and instead automatically pull the information using our directory, PKI, and MFA integrations to issue custom YubiKey FIPS credentials.
Do you need to issue YubiKey devices soon?
We would love to help. We know seeing is believing so schedule a virtual demo to see just how easy it is to encode a YubiKey.
Schedule YubiKey Demo
Focused on Secure Productivity
Multi-person controls, easy to use wizards, and simple to install software provides your workforce convenient and secure ways to encode their YubiKeys.
Self Service
The IdExchange self service portal makes it easy for your workforce to encode their YubiKey from anywhere they are located…even directly from a mobile phone.
Mobile Remote
The IdExchange self service portal makes it easy for your workforce to encode their YubiKey from anywhere they are located…even directly from a mobile phone.
Self Service
Mobile
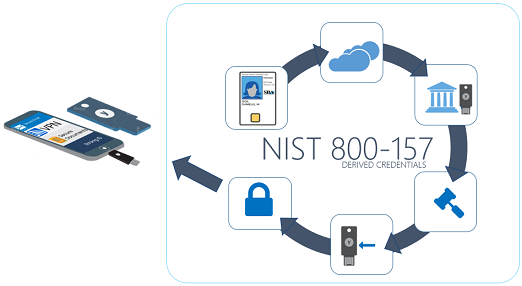
Helps Improve Existing Smart Card Programs
Add an easy-to-use form factor, mobile capabilities, and new authentication protocols, to an existing smart card infrastructure with no disruption risk.
Improve your current hardware MFA investments with the newest devices that support the widest range of authentication options while also ensuring compatibility with existing PKI infrastructure. Enable current card holders to easily issue their own YubiKey with the security processes defined by NIST.
Yubikey FIPS Device Registration
In the demonstration below, a PIV credential holder will register their Yubikey FIPS device in accordance with the NIST 800-157 derived credential requirements. They will first authenticate with their PIV credential, secure their Yubikey device and then register the Yubikey device for approval.