This YubiKey setup guide is for organizations experiencing sudden workforce location changes and still require hardware-based MFA. It is designed to handle unforeseen security circumstances associated with having to rapidly implement secure telecommuting including:
- The user cannot travel back to the company to pick up their security device.
- Company is unable to ship hardware MFA device to remote user.
- Company CA cannot be used because generating and emailing a PFX is forbidden.
- A user must be able to perform these tasks from their home or offsite location.
- Company requires MFA for remote services and passwords are not an option.
- Must be easy to purchase with a credit card in case company procurement process cannot be currently used.
At the end of this YubiKey setup process, the user will have a YubiKey with a securely generated, trusted certificate that can enable them to perform SSL, message signing, and email encryption – without any need for traveling or leaving their location.
What is required
Identity Proofing: The applicant must provide a valid email address. The system will email a onetime security code to this email address for the certificate retrieval.
*Note: To help our community the best way we can, we are offering the first 200 Sectigo certificates for free until May 1, 2020. We have provided external links to all of the products listed in this YubiKey setup guide so they can be further researched and purchased independently of CyberArmed. We have also provided questions and answers below with further resources that may help. We are simply providing these instructions in case they can help organizations address challenges they may have during this time.
YubiKey setup – Steps and Video Guide
The following steps will enable a YubiKey to be shipped directly to the user and then allow the user to securely load the YubiKey with a S/MIME and Authentication certificate. The video below shows the detailed steps.
- Order YubiKey Device from Yubico or Amazon. The YubiKey can be shipped directly to the user’s location.
- Prepare the workstation. Download and install the YubiKey Smart Card Minidriver and the YubiKey Manager to be able initialize and encode the YubiKey device.
- Request the certificate: The applicant enters their name and email information for the certificate.
- Collect the certificate: In this phase, the applicant uses a one-time code to begin the process. The keys are securely generated on the YubiKey device and the CA returns a certificate comprised of the public key.
Questions / Answers
Q: Why does this guide use YubiKey?
A: The YubiKey is very easy to get into the hands of users fast. It can be purchased from large online retailers and be delivered directly to their location. The YubiKey software is also easy to obtain and install. It is also supported by the HID Credential Management System, IdExchange, Axiad Cloud, and Duo Security so it can be used across the enterprise when hardware MFA tokens are required.
Q: Why does this YubiKey setup guide use the Sectigo CA?
A: Sectigo is easy to purchase and is trusted on Windows platforms. We are also able to provide 200 free certificates. The Sectigo CA has issued over 100 million certificates and is used by the Fortune 1000 companies. It also has reliable validation. If a higher assurance CA is preferred, the IdenTrust CA can also be used.
Q: How can this be secure? It is not my CA!
A: While we fully understand it is preferable to use the organization’s certificate authority, this process is for when the CA cannot be used but the organization needs to find a way to continue to use PKI/crypto for MFA. However, the process is still secure because of the following:
- Identity Verification: The user must be registered with their email address. When the user is approved, they must be able to login to their email and retrieve a security code to be able to encode their certificate.
- Private Key Storage in a Hardware Device: The private key is generated in the YubiKey and is non-exportable. Therefore, the private key will only ever be on the YubiKey device (no one but the user will ever be able to use that private key).
- Certificate Registration: The company still must register the certificate with their authentication system so that it can be used with corporate resources.
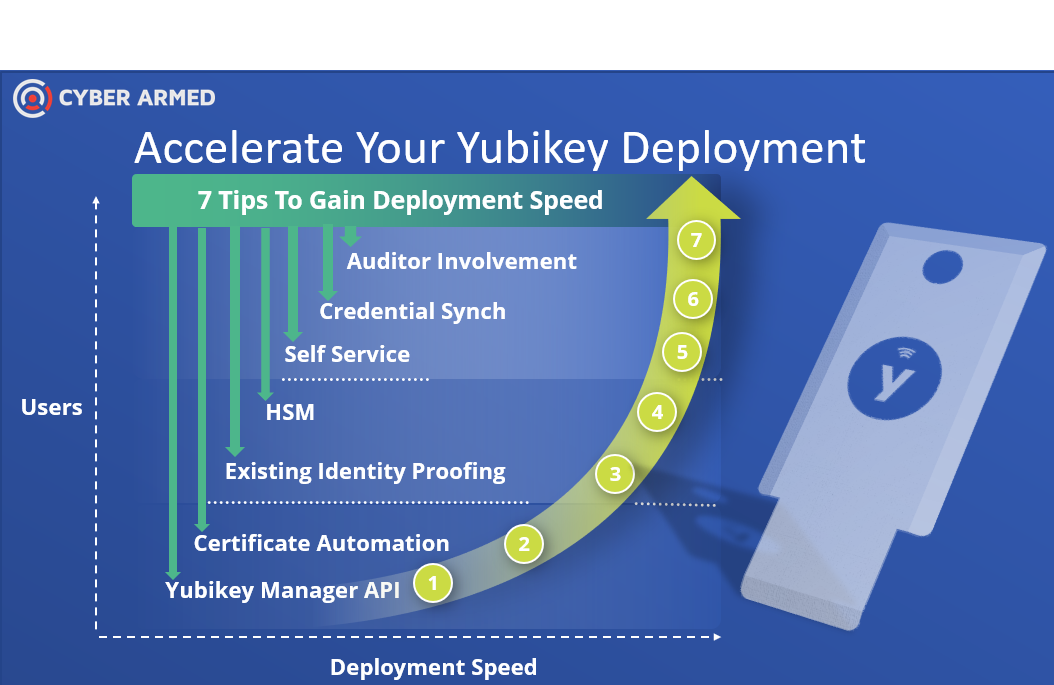
Q: How can we use our own CA and YubiKey for remote issuance?
A: See our YubiKey Tips blog here. It provides information how to set up the Microsoft CA with YubiKey. If you have a different CA, please contact support@cyberarmed.com and we can send you documentation.
Q: If we purchase the YubiKey at Amazon, can we use it with our CA?
A: Yes. The YubiKey can be reset to factory settings. The YubiKey can then encoded with the corporate badging system.
Q: In the video, why are you using IE 11 and not Edge, Chrome, or Firefox
A: To use the free software, IE11 is the only browser that is currently capable of interacting properly with the YubiKey and CA.
Q: Does CyberArmed store any data?
A: The First Name, Last Name, and Email address is stored in the Sectigo CA so we can approve or deny the request as well as revoke the certificate. This data is stored in the Sectigo CA, we do not store it in a CyberArmed system. If you prefer, you can purchase the certificates directly from Sectigo. The goal for us is to help organizations that may need assistance, we are not trying to collect information.
Q: I have the HID CMS that is already connected to my CA. How can I set it up to issue remotely?
A: Yes. We are currently developing a blog on this. If you need immediate assistance, send us an email at support@cyberarmed.com and will send you guidance.
Q: What happens to the certificate once we restore normal operations
A: The certificate can continue to be used or can be revoked. To revoke, please send an email to support@cyberarmed.com with “REVOKE” in the subject and provide the email address or order number.
Q: This certificate will allow me to encrypt email, is my key being archived elsewhere?
A: No, the encryption key is not being archived. The private key is only on the Yubikey and not anywhere else. No one but the person that has the Yubikey and knowledge of the PIN to the YubiKey will be able to use the encryption key.
Conclusion
We understand that rapidly implementing a remote issuance model for hardware devices is extremely challenging. We hope this guidance can provide information how you can still find a way to perform YubiKey setup for remote users to keep your defenses strong with hardware MFA. with even with a rapid change in workforce placement. Stay safe and just email us at support@cyberarmed.com if you have any questions.

 @CyberArmed
@CyberArmed